1. What is a technique used by the APT to both perform recon and gain initial access?
Spearphishing Link is a technique used by APT28 in both the Reconnaissance and Initial Access phases.
- In the Reconnaissance phase, attackers send crafted links to gather user credentials or organizational information.
- In the Initial Access phase, the stolen credentials are used to gain entry into the target network.
This makes T1598.003 – Spearphishing Link a key technique that serves dual purposes in the attack lifecycle.
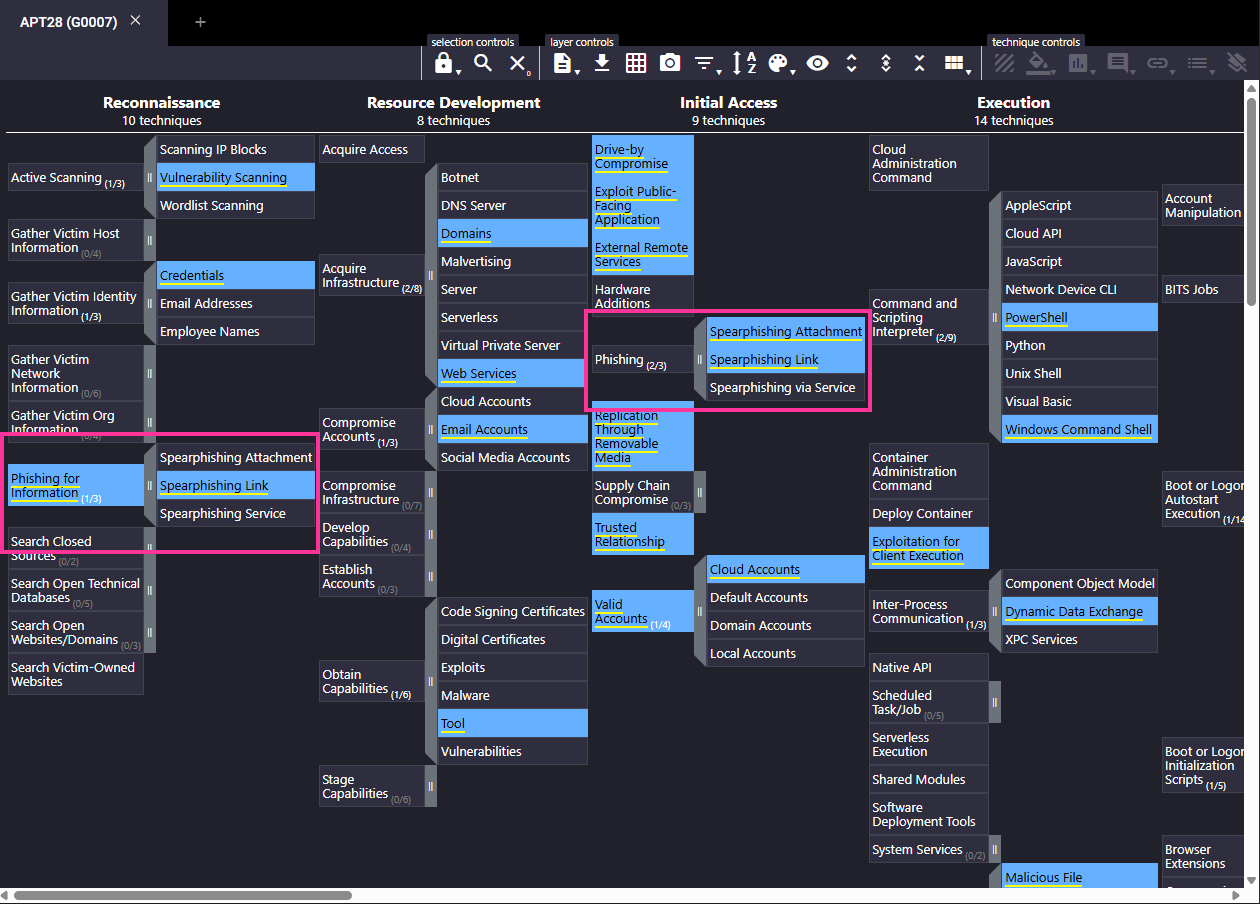
Spearphishing link
2. Sunny identified that the APT might have moved forward from the recon phase. Which accounts might the APT compromise while developing resources?
- This technique falls under the Resource Development tactic.
- APT28 compromises existing user accounts (e.g., email accounts) to:
- Send phishing emails from trusted sources
- Deliver malware
- Maintain a believable identity for further access attempts
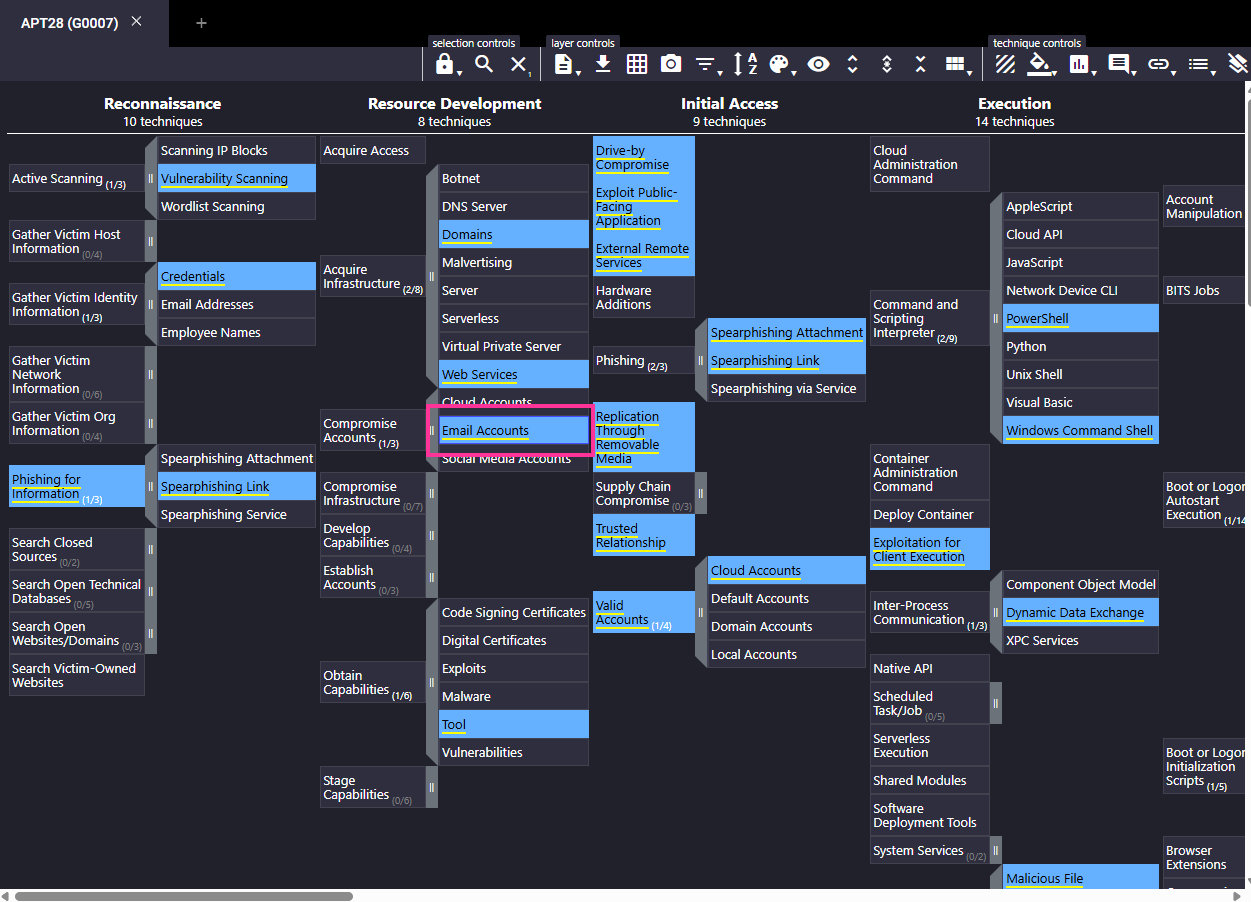
Email accounts
3. E-corp has found that the APT might have gained initial access using social engineering to make the user execute code for the threat actor. Sunny wants to identify if the APT was also successful in execution. What two techniques of user execution should Sunny look out for? (Answer format: <technique 1> and <technique 2>)
APT28 often uses social engineering to trick users into:
- Clicking malicious links (
T1204.001) - Opening malicious attachments/files (
T1204.002)
These techniques fall under the User Execution category in the Execution tactic and are commonly used by APT28 for initial foothold.
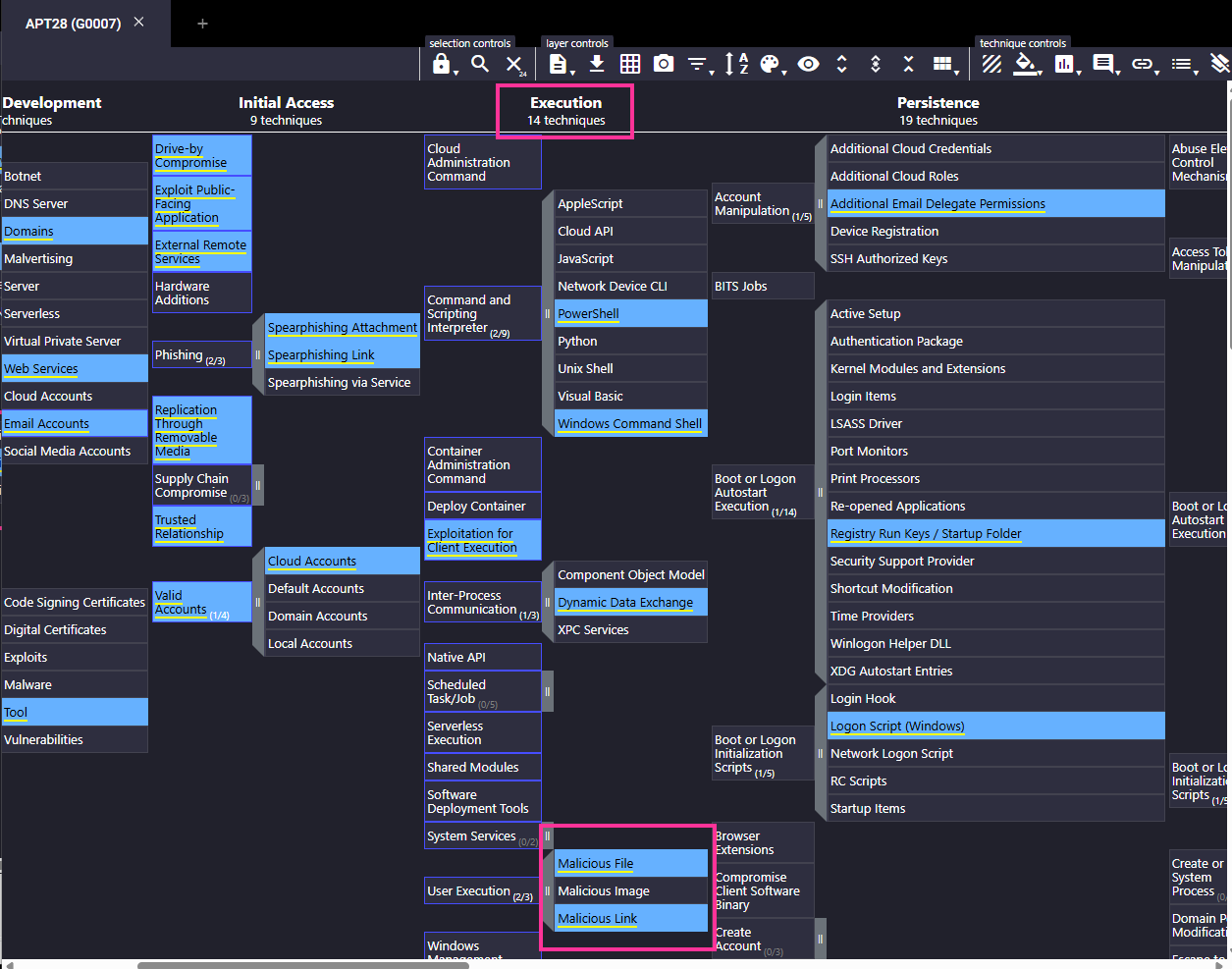
Malicious file and malicious link
4. If the above technique was successful, which scripting interpreters should Sunny search for to identify successful execution?
If the malicious file or link was executed successfully, APT28 may have used scripting interpreters to run payloads. The relevant techniques are:
- T1059.001 – PowerShell
- T1059.003 – Windows Command Shell (cmd.exe)
These are commonly used by APT28 for executing scripts and furthering compromise after initial access.
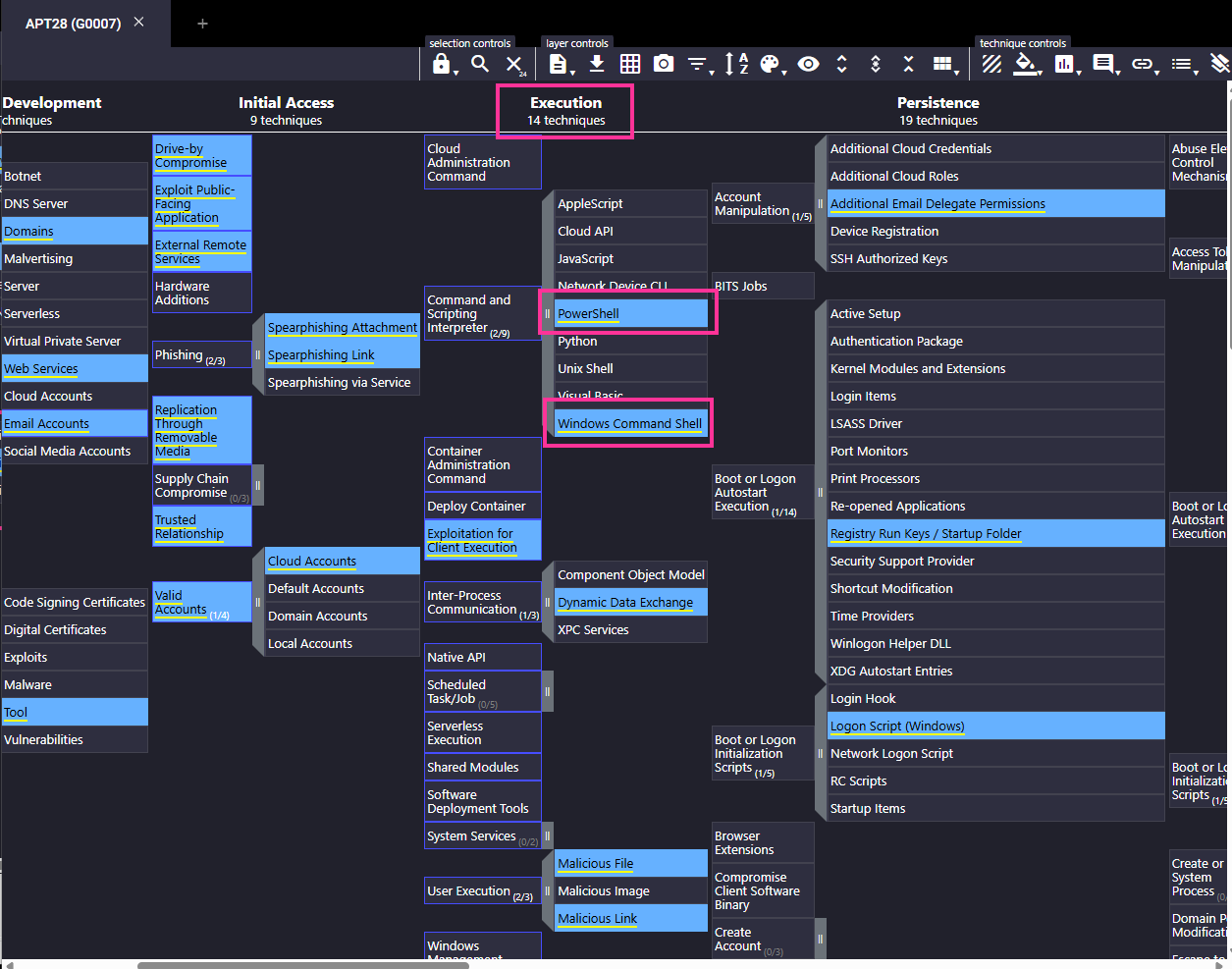
Powershell and Windows Command shell
5. While looking at the scripting interpreters identified in Q4, Sunny found some obfuscated scripts that changed the registry. Assuming these changes are for maintaining persistence, which registry keys should Sunny observe to track these changes?
APT28 often uses registry run keys to maintain persistence on a compromised system. These keys allow scripts or executables to automatically run when a user logs in or the system starts.
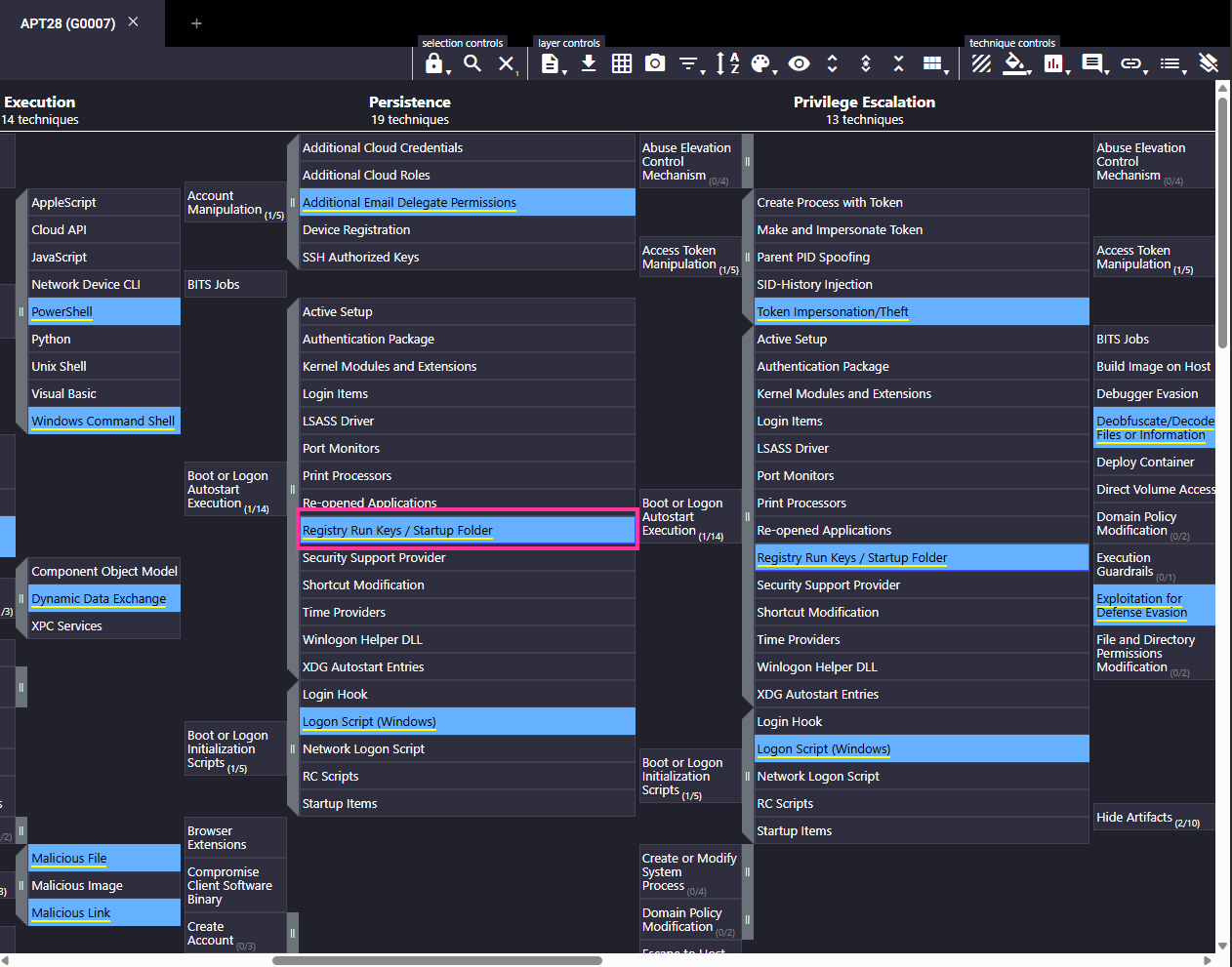
Registry run keys
6. Sunny identified that the APT executes system binaries to evade defences. Which system binary’s execution should Sunny scrutinize for proxy execution?
APT28 has been observed using rundll32.exe, a legitimate Windows system binary, to proxy the execution of malicious DLLs while evading detection.
This technique is part of:
- T1218.011 – Signed Binary Proxy Execution: Rundll32
Using rundll32.exe allows the attacker to run code without dropping suspicious executables, helping them bypass security controls like antivirus or EDR.
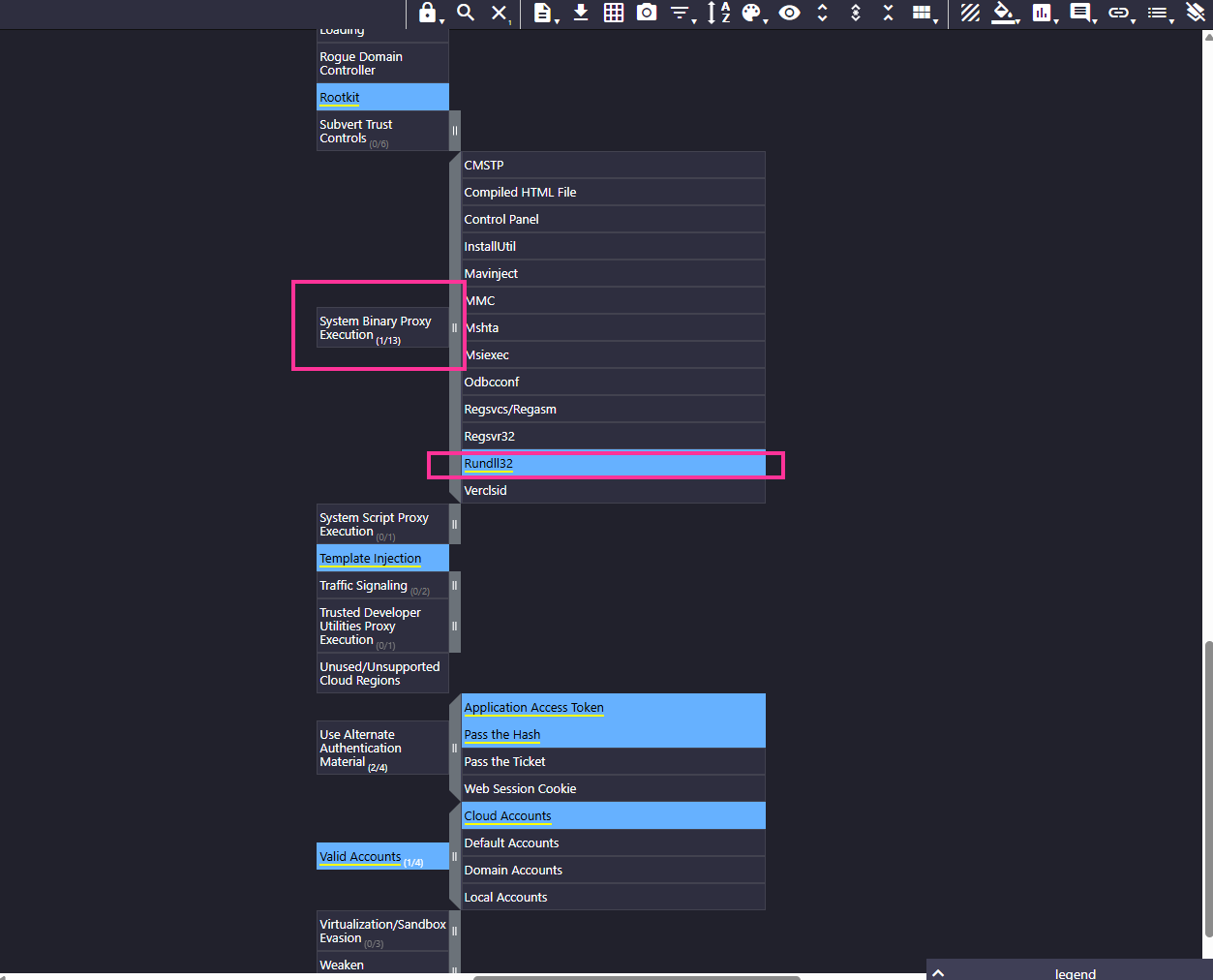
Rundll32
7. Sunny identified tcpdump on one of the compromised hosts. Assuming this was placed there by the threat actor, which technique might the APT be using here for discovery?
Tcpdump is a legitimate network packet capture tool. If Sunny finds it on a compromised host and it wasn’t installed by IT, it’s likely being abused by the attacker to monitor network traffic, including credentials, tokens, or lateral movement activity.
This aligns with:
- T1040 – Network Sniffing
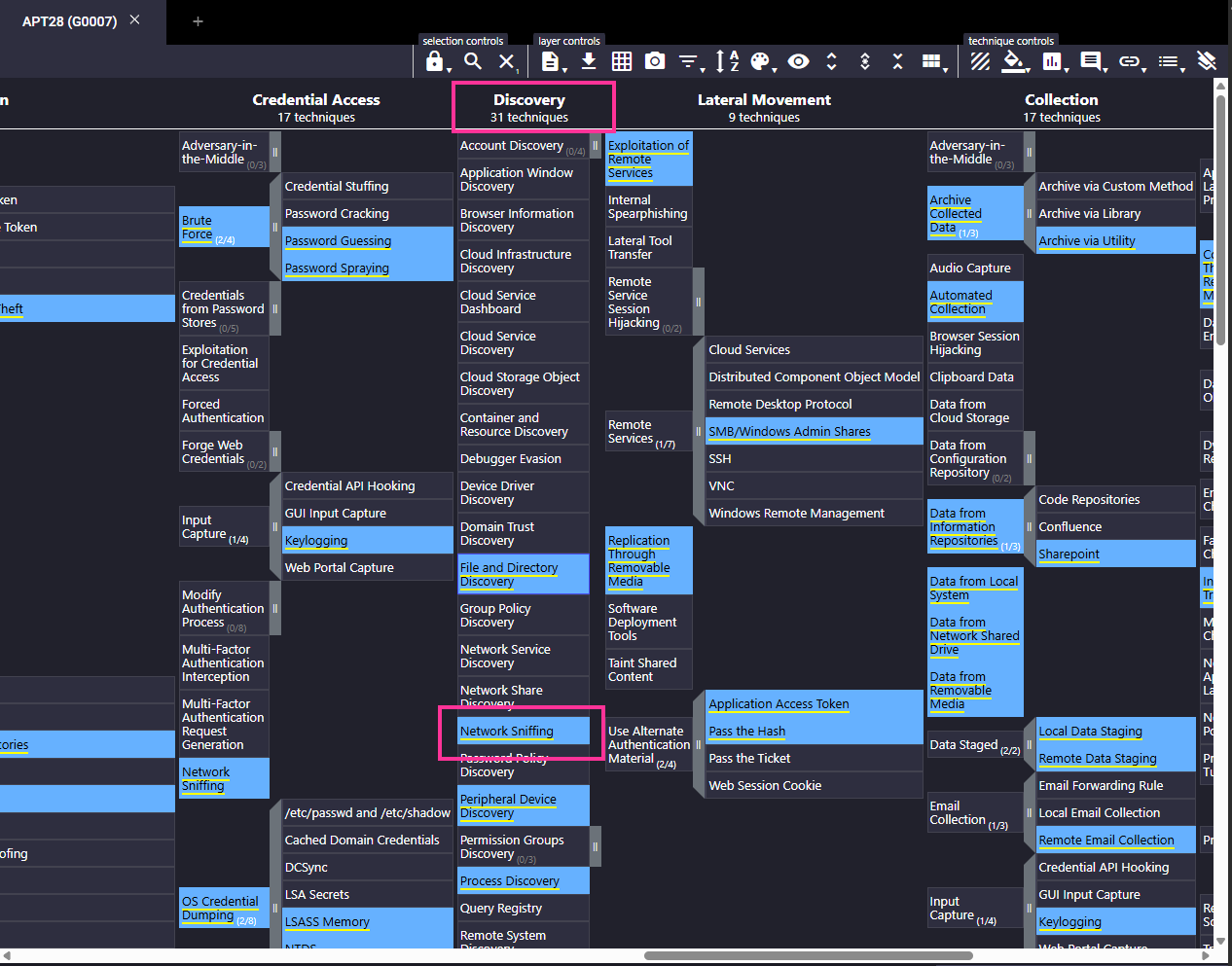
Network sniffing
8. It looks like the APT achieved lateral movement by exploiting remote services. Which remote services should Sunny observe to identify APT activity traces?
APT28 has been observed performing lateral movement by exploiting remote services, especially:
- SMB (Server Message Block)
- RPC (Remote Procedure Call)
These are commonly used in:
- T1210 – Exploitation of Remote Services
- T1021.002 – SMB/Windows Admin Shares
- T1021 – Remote Services
APT28 may exploit vulnerabilities like MS17-010 (EternalBlue) or abuse admin shares and services over SMB/RPC to move laterally within the network.
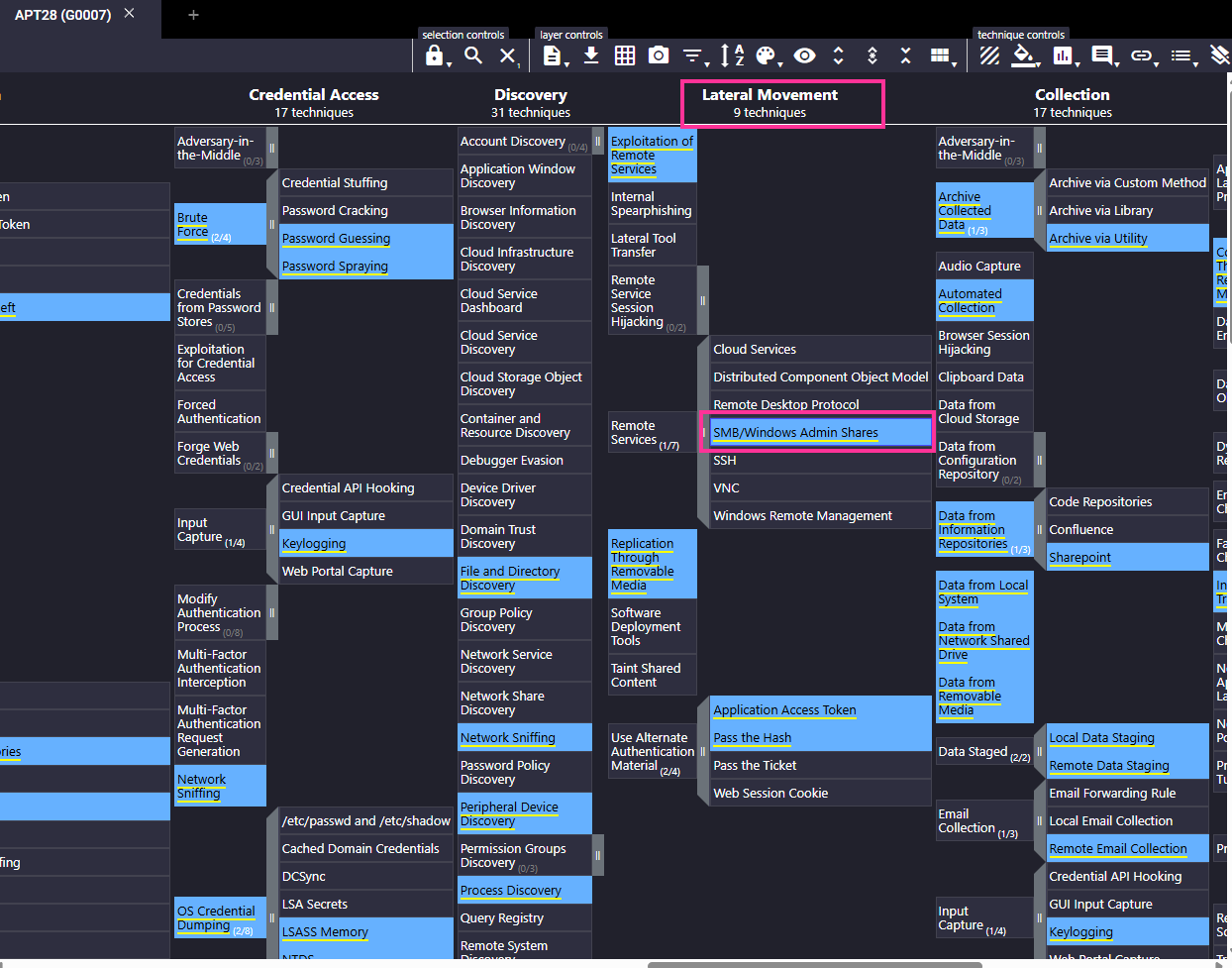
SMB/Windows Admin shares
9. It looked like the primary goal of the APT was to steal intellectual property from E-corp’s information repositories. Which information repository can be the likely target of the APT?
APT28 has been documented targeting information repositories to steal sensitive data. One specific target mentioned in MITRE ATT&CK data is:
- T1213.002 – SharePoint
APT28 has collected information from Microsoft SharePoint services within victim networks.
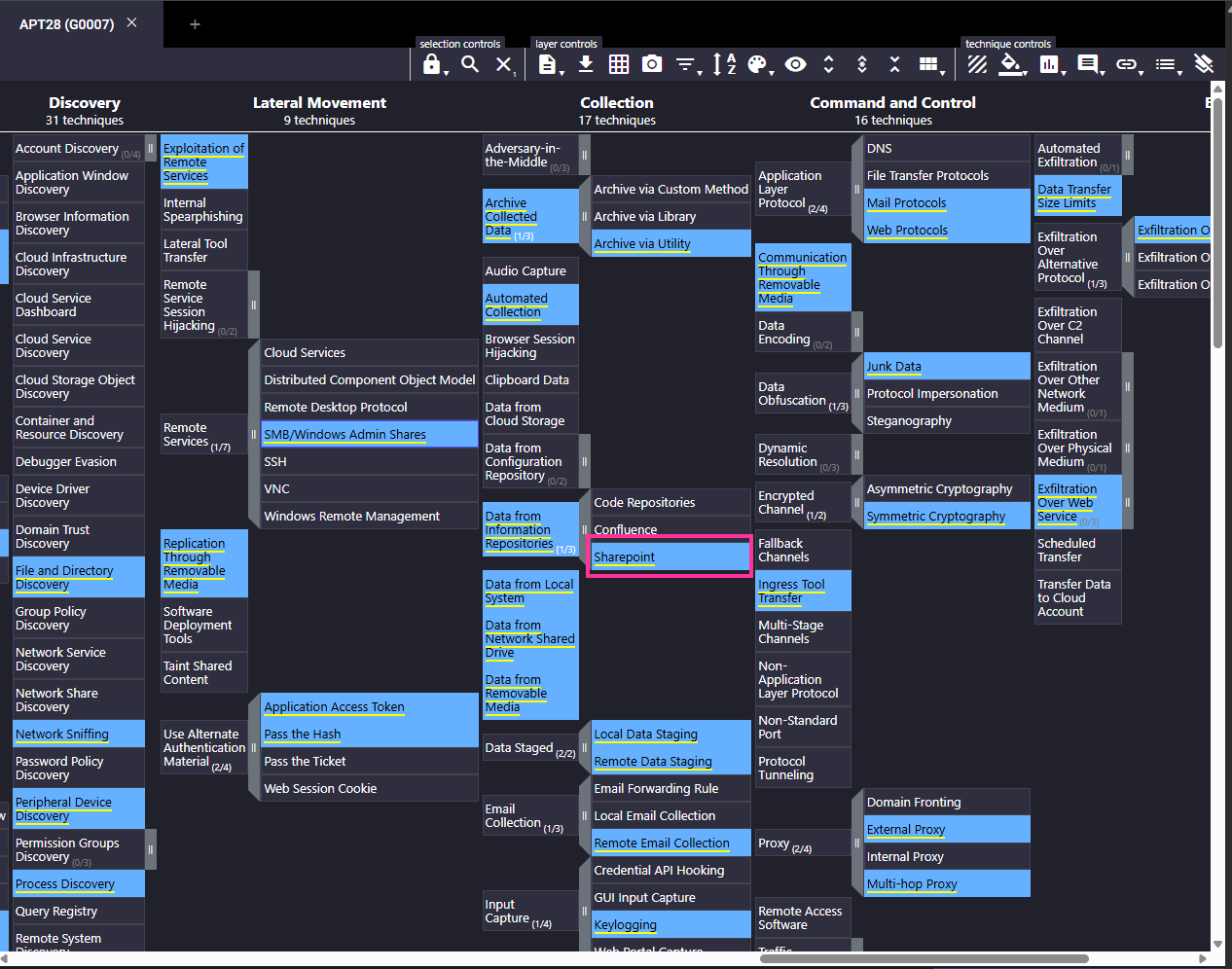
Sharepoint
10. Although the APT had collected the data, it could not connect to the C2 for data exfiltration. To thwart any attempts to do that, what types of proxy might the APT use? (Answer format: <technique 1> and <technique 2>)
To bypass restrictions and exfiltrate data when a direct connection to the Command and Control (C2) server fails, APT28 may use the following proxy techniques:
- External Proxy (T1090.002):
- The APT routes traffic through external proxy servers, such as compromised web servers or commercial proxy/VPN services, to mask their C2 infrastructure.
- Multi-hop Proxy (T1090.003):
- The APT chains multiple proxies together — for example, using several infected systems or relays (including VPNs or Tor) — to further obscure the origin of the traffic.
These proxy methods help attackers evade detection, blend in with legitimate traffic, and ensure successful exfiltration attempts.
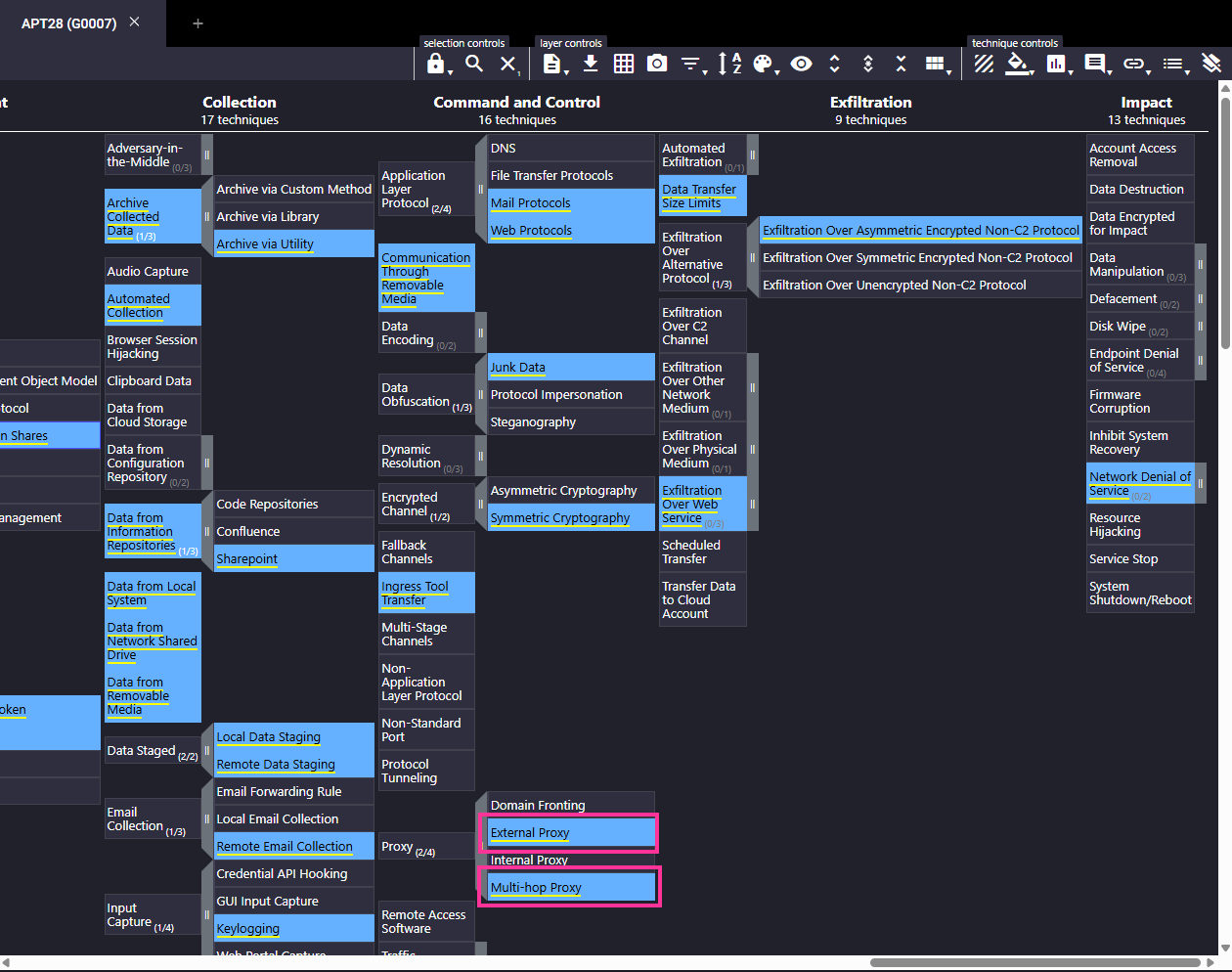
external proxy and multi-hop proxy
Congratulations! You have helped Sunny successfully thwart the APT’s nefarious designs by stopping it from achieving its goal of stealing the IP of E-corp.

