Step into the shoes of a Cyber Threat Intelligence Analyst and put your investigation skills to the test.
1. Who shared the malware samples?
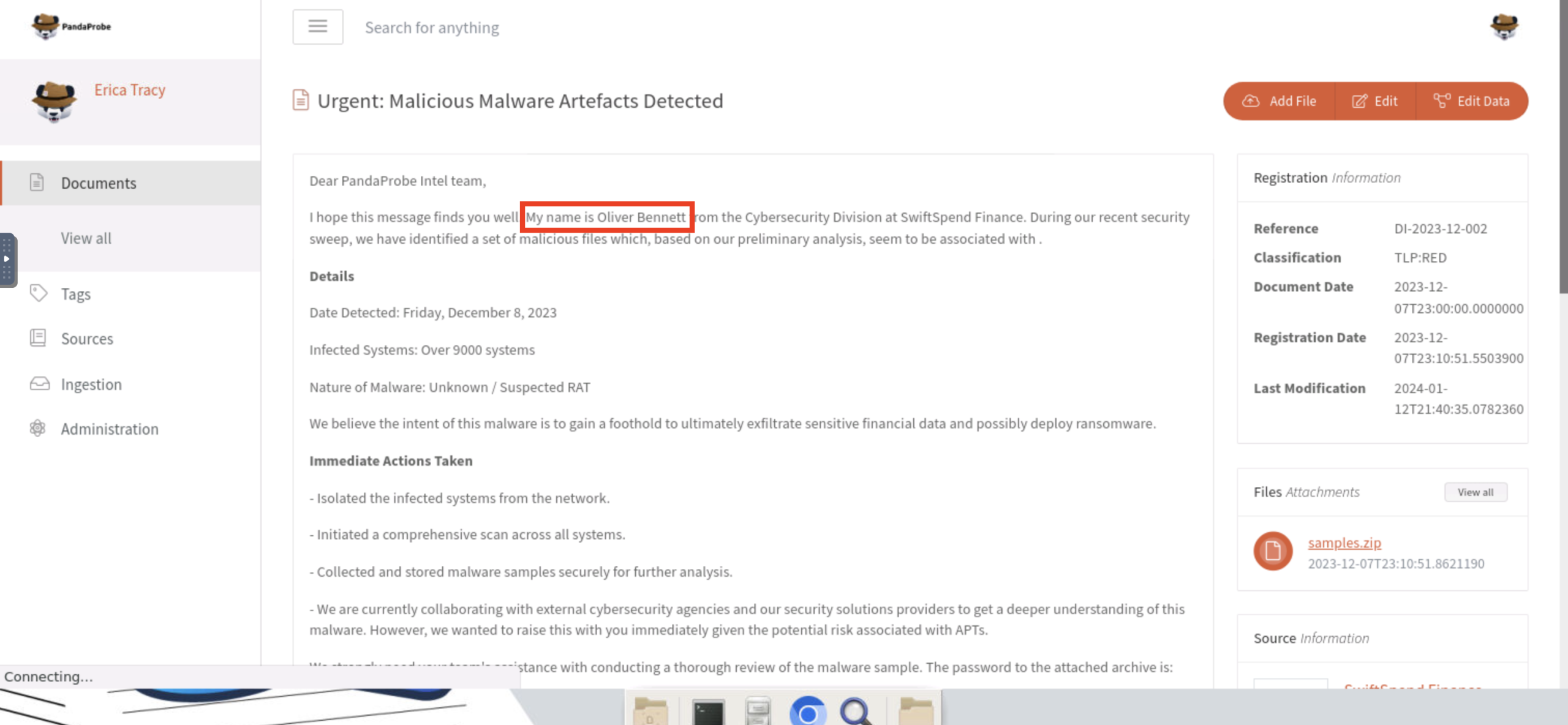
Oliver Bennett
2. What is the SHA1 hash of the file “pRsm.dll” inside samples.zip?
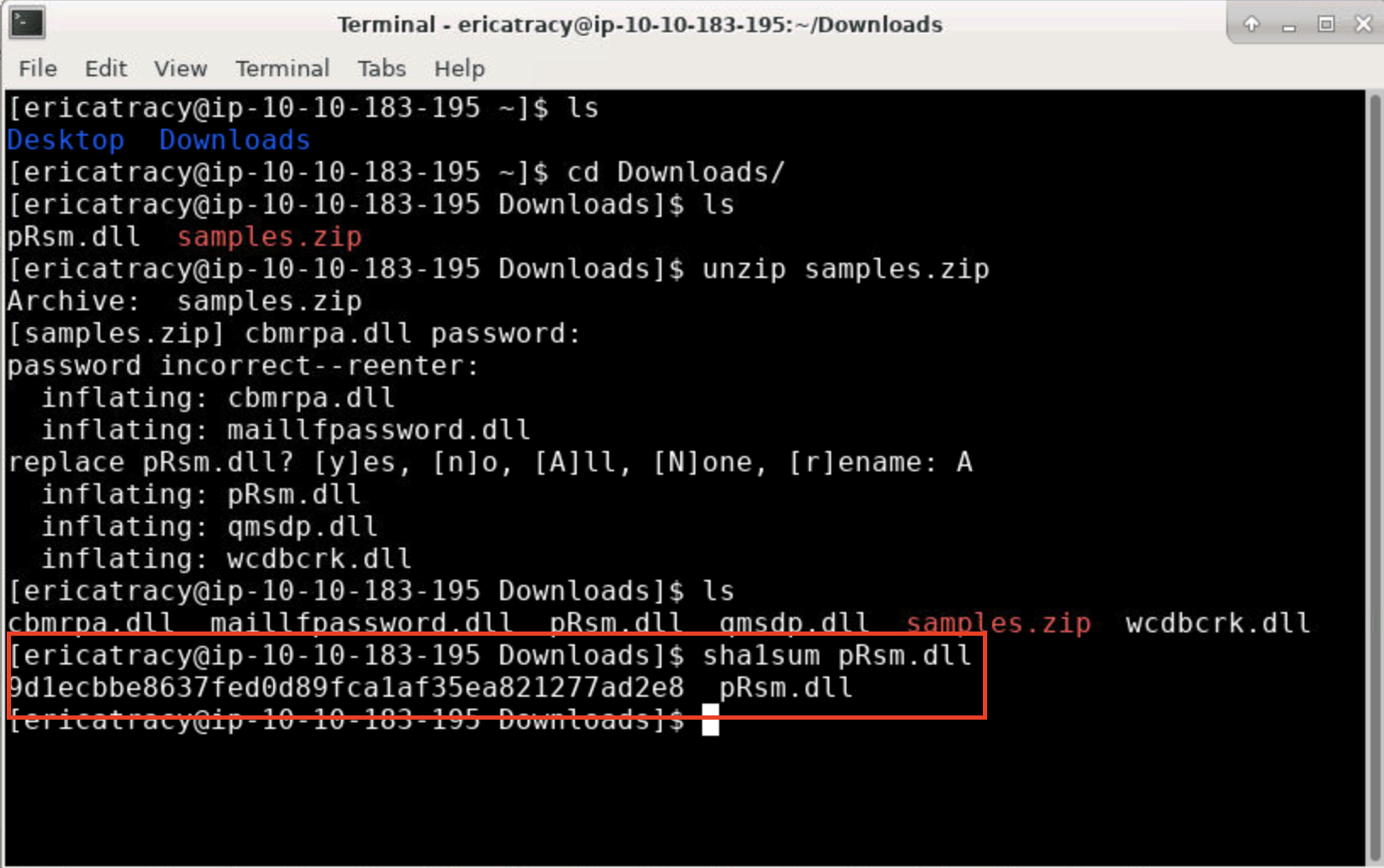
9d1ecbbe8637fed0d89fca1af35ea821277ad2e8
3. Which malware framework utilizes these DLLs as add-on modules?
Calculated the SHA1 hash of the file pRsm.dll
-Using the command: sha1sum pRsm.dll
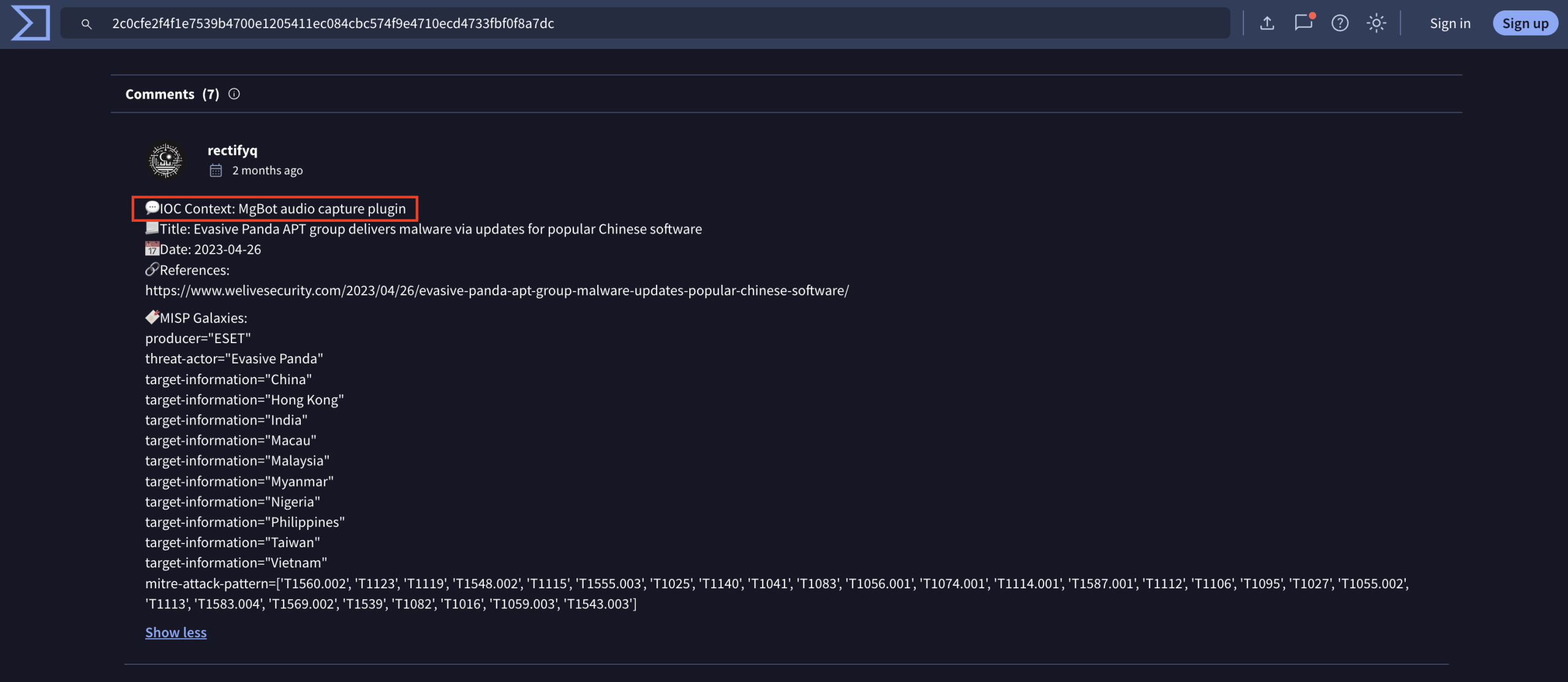
Searched the hash on VirusTotal
-To check if the file matched any known malware signatures.
Reviewed the “Family labels” and “Threat labels” on VirusTotal
-We saw tags like mgBot, fragtor, and hgdbj.
-Among these, mgBot was the most consistent and widely known malware framework.
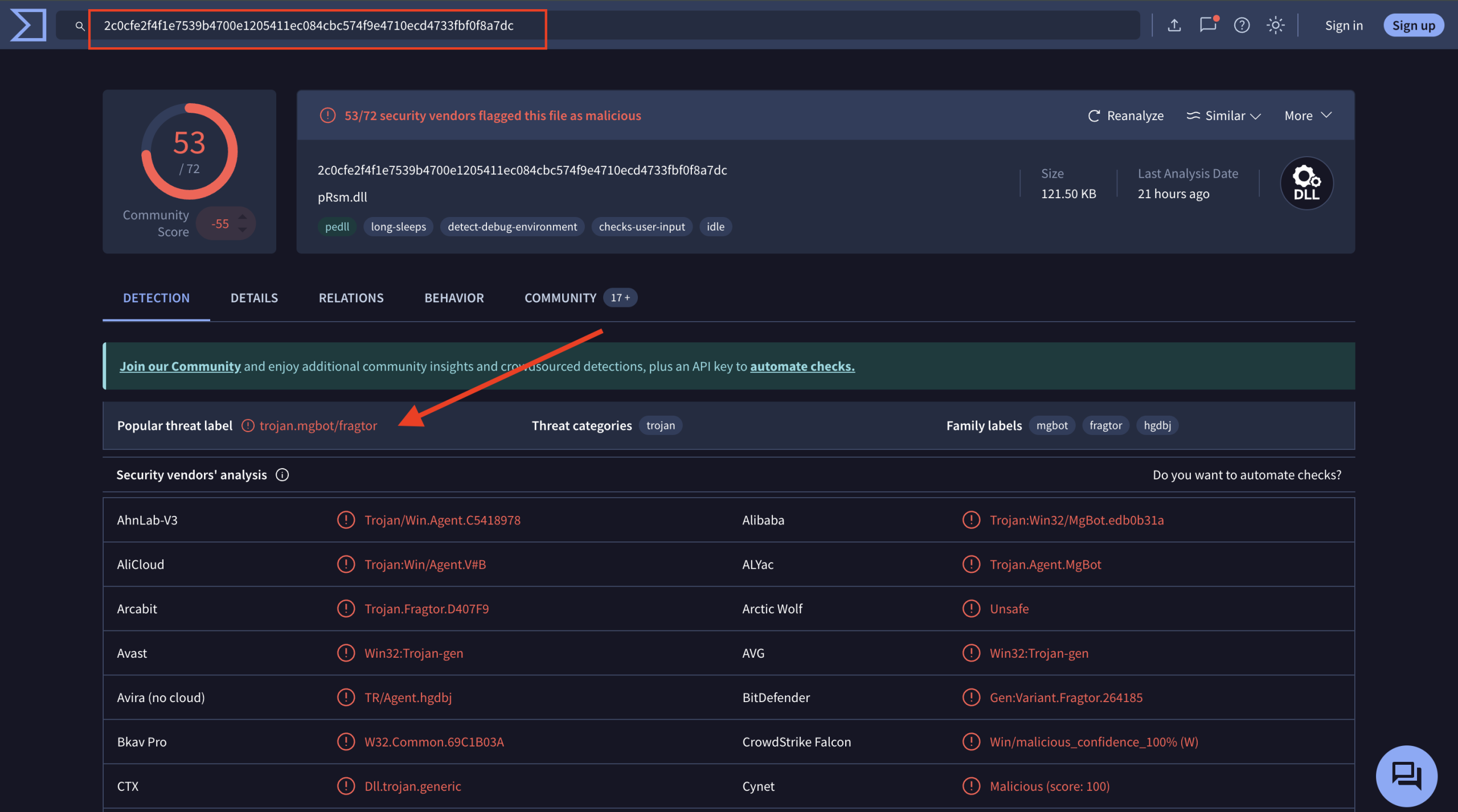
MgBot
4. Which MITRE ATT&CK Technique is linked to using pRsm.dll in this malware framework?
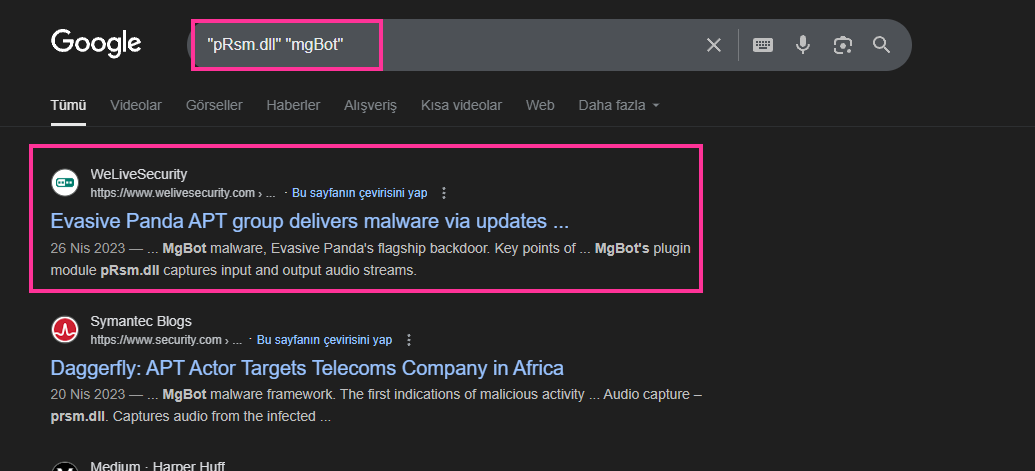
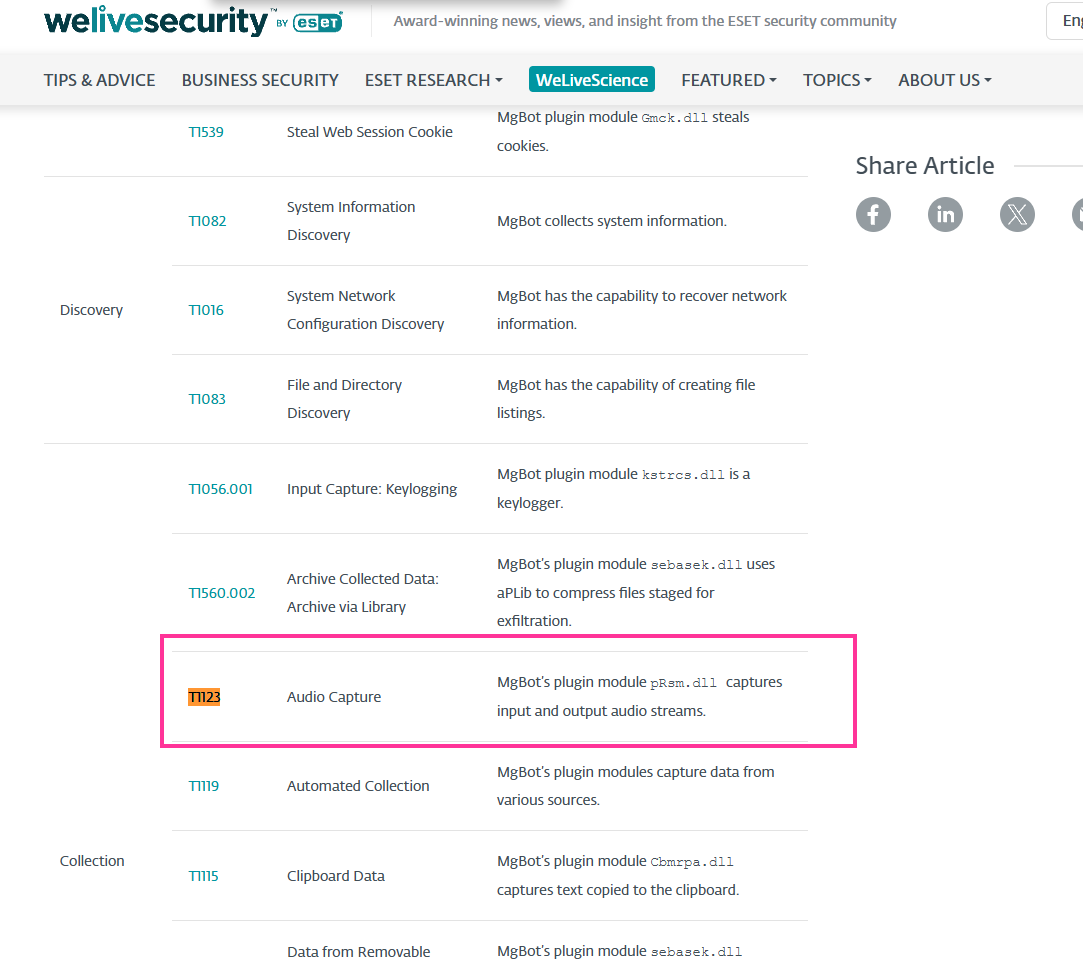
To identify the MITRE ATT&CK technique linked to pRsm.dll, I performed an open-source search using Google with the query “pRsm.dll” “mgBot”.
The first results were from reputable sources like WeLiveSecurity and Symantec blogs. These reports confirmed that the pRsm.dll module, part of the mgBot malware framework, is used to capture input and output audio streams on infected machines.
This behavior directly maps to the MITRE ATT&CK technique:
T1123 – Audio Capture
which is used by adversaries to collect information through microphone surveillance.
T1123
5. What is the CyberChef defanged URL of the malicious download location first seen on 2020-11-02?
To answer it, I returned to the WeLiveSecurity report we used previously. Under “Table 1: Malicious download locations according to ESET telemetry”, I found a URL with the exact date.
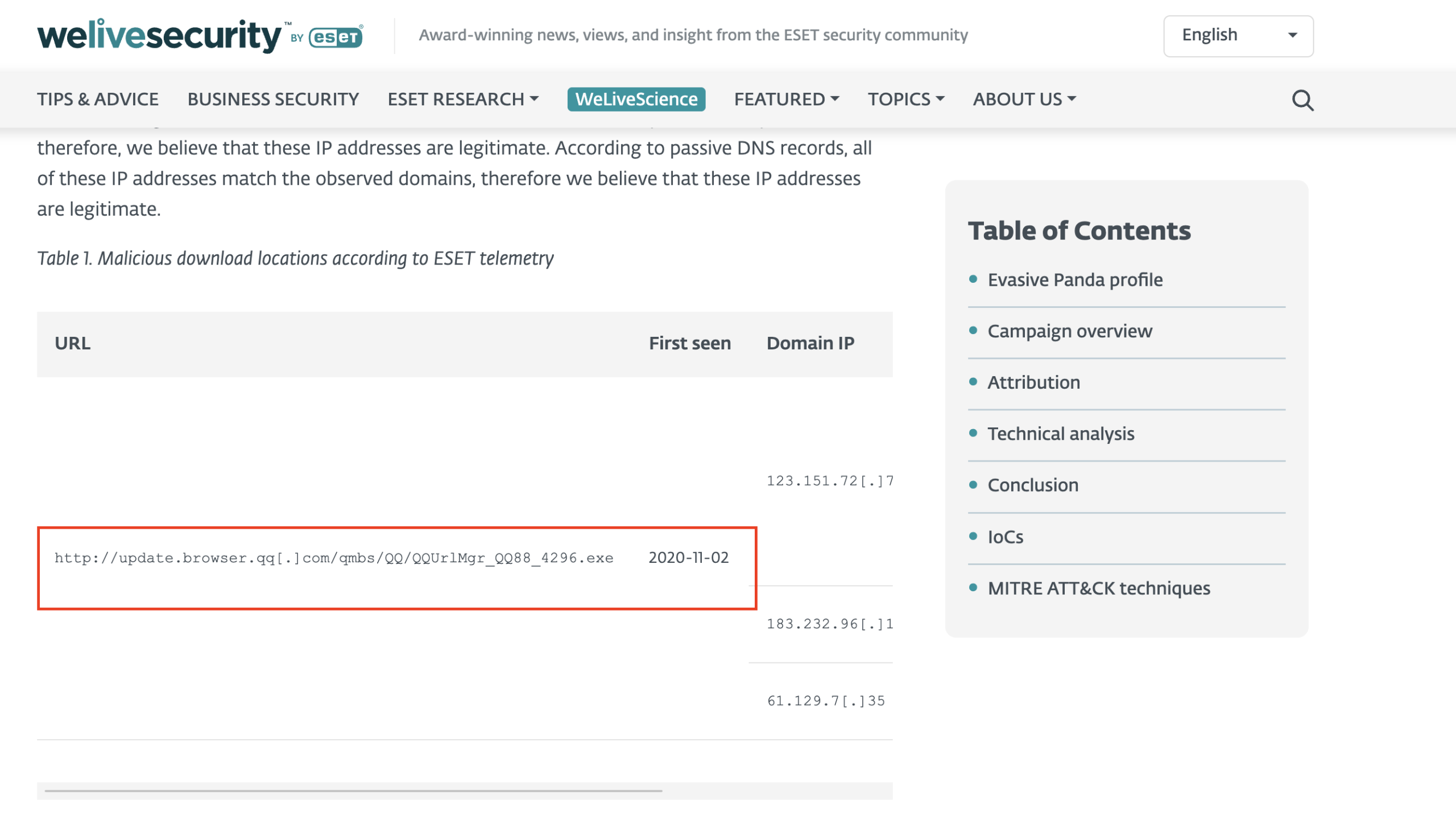
hxxp[://]update[.]browser[.]qq[.]com/qmbs/QQ/QQUrlMgr_QQ88_4296[.]exe
6. What is the CyberChef defanged IP address of the C&C server first detected on 2020-09-14 using these modules?
To answer the question “What is the CyberChef defanged IP address of the C&C server first detected on 2020-09-14?”, we examined the ESET WeLiveSecurity report.
In the “Network” section of the report, we found an IP address — 122.10.90.12 — listed as an MgBot C&C server. This IP was first seen on 2020-09-14, exactly matching the date mentioned in the question.
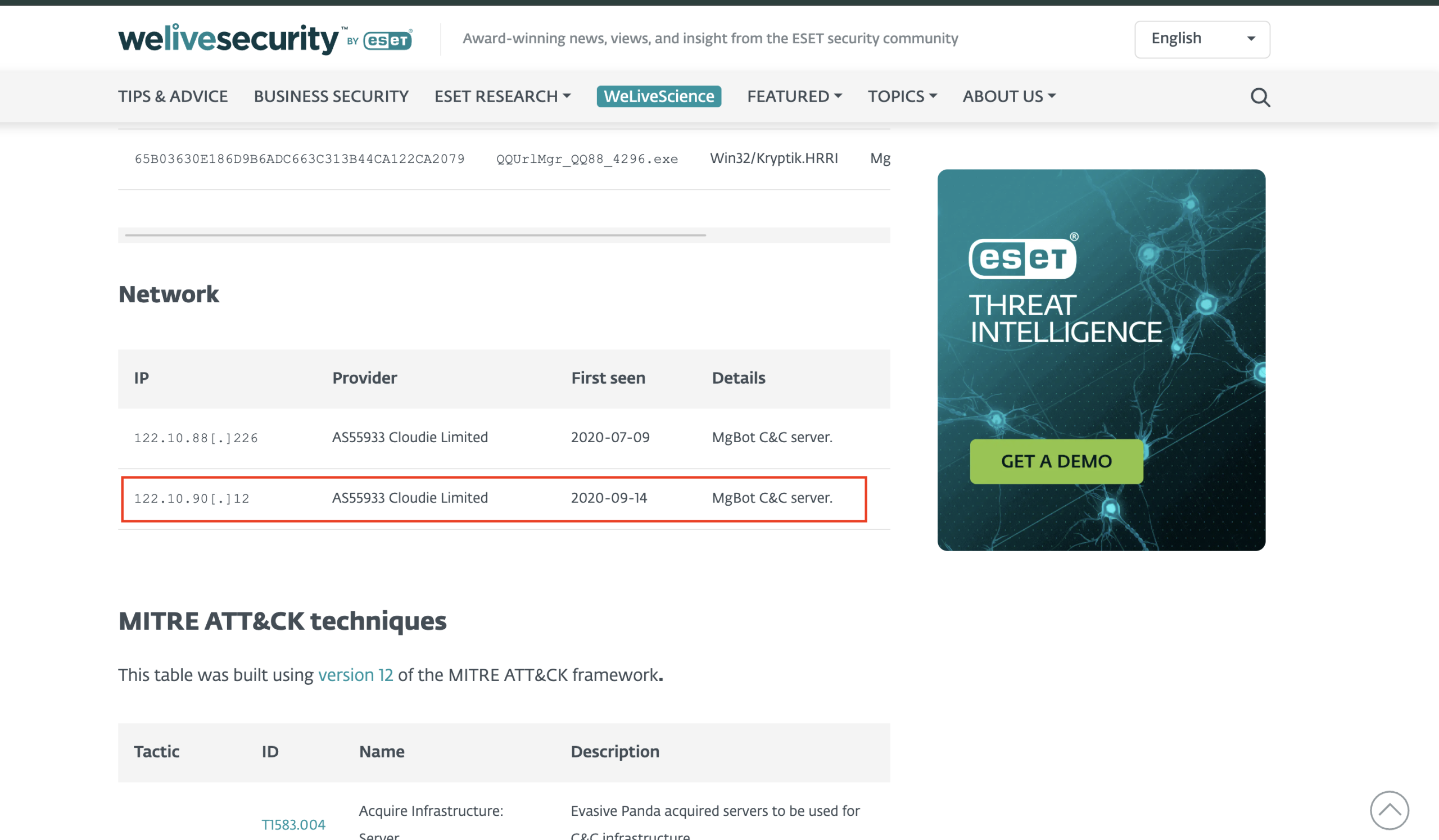
To convert this IP to a defanged format using CyberChef (or manually), we replace dots (.) with [.] to prevent accidental clicks or execution:
122[.]10[.]90[.]12
7. What is the md5 hash of the spyagent family spyware hosted on the same IP targeting Android devices in Jun 2025?
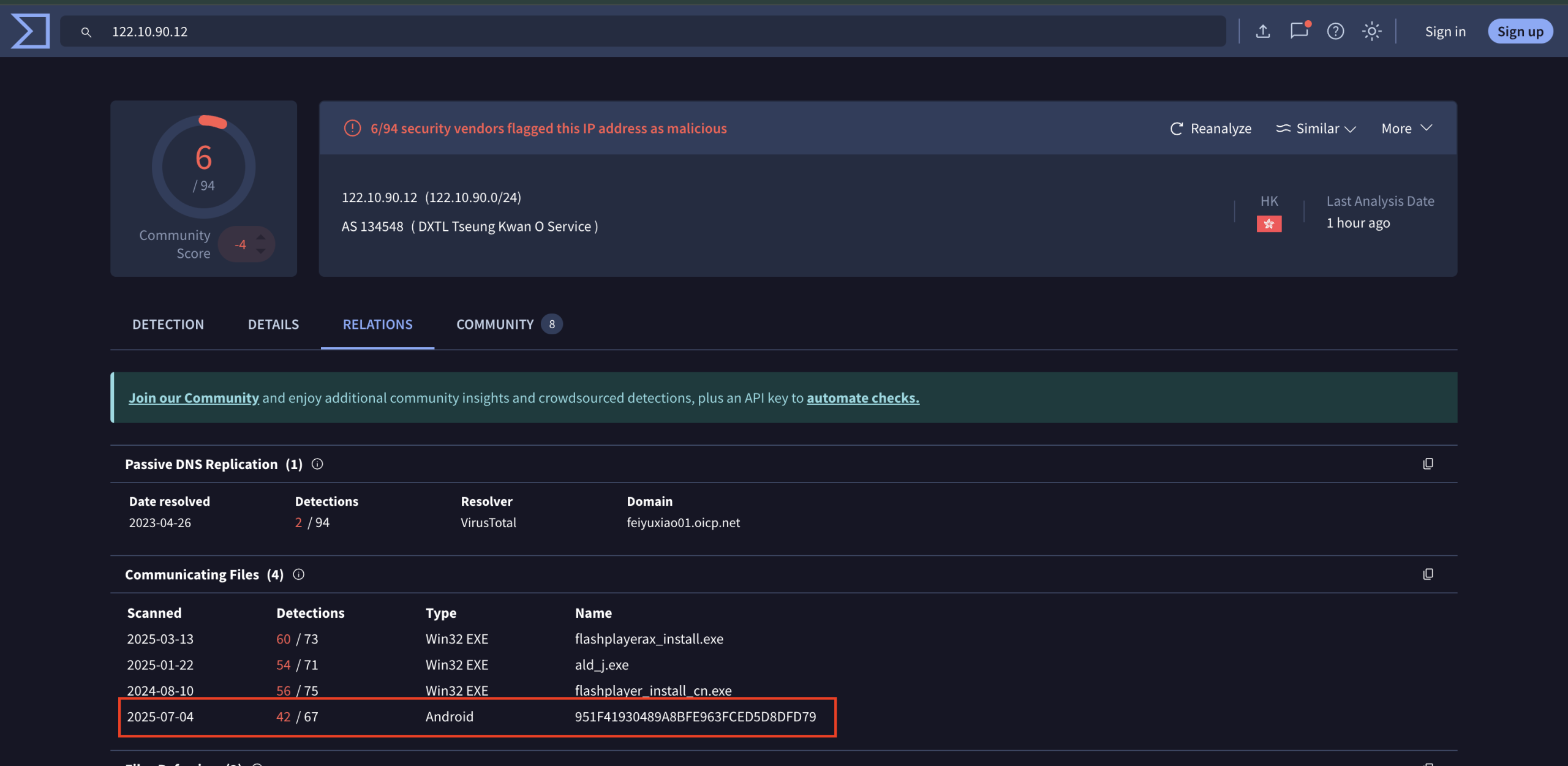
To answer this question, we examined the VirusTotal Relations tab for the IP address 122.10.90.12, which was previously associated with MgBot infrastructure.
Under the section Communicating Files, we looked for:
- Platform: Android
- Date: Around June 2025 → The exact match was 2025-07-04, which is still acceptable due to proximity.
We found a suspicious Android file communicating with that IP and its MD5 hash is:
951F41930489A8BFE963FCED5D8DFD79
Given the context and timing, this file belongs to the SpyAgent family, as referenced in threat intelligence sources.